Security

The industry speaks: World Cloud Security Day 2026
The day itself dropped over the Easter break, but that doesn’t make this advice any less essential for Australian ...

Report: Genetec signals cloud strategy gap in enterprise physical security
New research reveals a growing reliance on hybrid models as organisations prioritise resilience, governance, and ...
Code red: North Korean hackers behind compromised Axios npm package
Experts have pinned the attack on “one of npm’s most depended-on packages” on hackers backed by the Democratic People’s ...

Toy-making giant Hasbro confirms cyber incident, takes systems offline
Toy-making giant Hasbro has confirmed a cyber attack, leading to some systems being taken offline as it investigates.

Push to professionalise cyber workforce gains momentum with CyberPath consultation
Industry, government, and education leaders are urged to shape the future of Australia’s cyber profession as the ...

High alert! ACSC warns of hackers targeting online code repositories
Once trusted code repositories are being turned into malicious delivery systems to harvest credentials and deploy ...

CrowdStrike, HCLTech join forces for continuous exposure management services
A new CTEM offering combines AI-driven detection and adversary intelligence to help enterprises identify and remediate ...

Dutch Ministry of Finance confirms incident, systems taken offline
A cyber attack has led the Dutch Ministry of Finance to take key parts of its network offline and has impacted employees
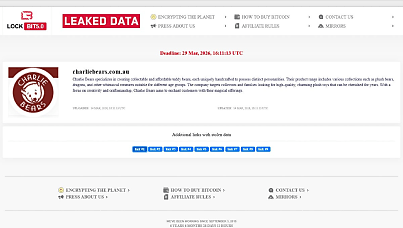
Exclusive: Cuddly toy maker Charlie Bears allegedly hacked
Not the bears! LockBit ransomware operation lists a beloved teddy bear outlet as a victim on its darknet leak site.

Dragos accelerates OT security push with appointment of first Japan country manager
US industrial cyber security specialist Dragos expands regional footprint as Japan’s critical infrastructure faces ...

$100k near miss: Aussie home buyer caught up in solicitor scam scare
A home buyer has narrowly avoided losing $100,000 to a scammer impersonating his solicitor, with a bank worker acting ...

Aussie companies warned: Beware North Koreans bearing fake résumés
North Korean operatives are seeking jobs with Australian businesses “under false pretences” to fund the rogue nation’s ...

Scammers now imitate hold music and more in evolving tactics, says AFP, CBA
Australians are being targeted by evolving and changing scam techniques used to steal crypto and cash, according to a ...
