The group focuses largely on small- to medium-sized businesses, demanding ransoms of between US$200,000 and US$4 million.
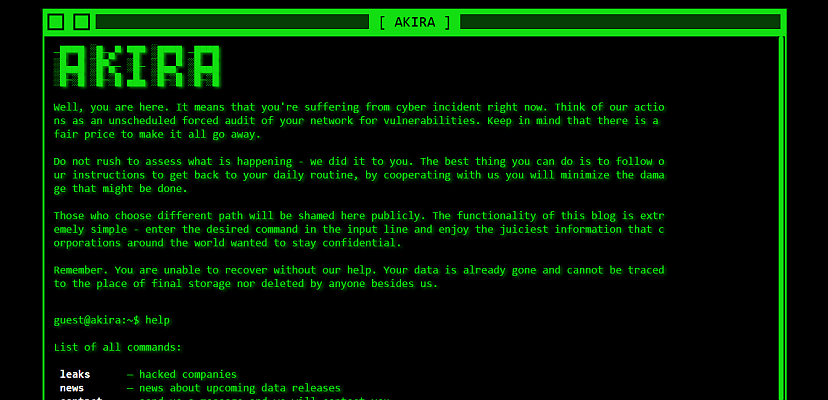
Akira also has a thing for retro computing – the group’s darknet leak seat is in 80s-themed black and green and is navigated by a command-line interface. It’s probably not the most useful thing a possible victim wants to see when they begin negotiations, but we guess Akira likes it that way.
Nonetheless, the group is active and effective enough that the US Health Sector Cybersecurity Coordination Center (HSCCC) recently released an in-depth report on its operations and tactics. According to the HSCCC report, even though Akira is a relatively new operator, it also has quite a bit of technical and financial overlap with the disbanded Conti group.
Akira tactics, techniques, and procedures
Akira ransomware comes in two flavours, Windows and Linus, and both are 64-bit applications.
The Windows version is written in C++ and uses an RSA-4096 cipher with a symmetric key, and it takes advantage of the Windows CryptoAPI. The Linux version, on the other hand, is aimed at VMware ESXi servers and uses the Crypto++ library. Otherwise, both versions are similar in operation and avoid encrypting certain files, such as .exe, .lnk, and .sys, among others.
Researchers have noted that neither version is particularly advanced but are somewhat customisable.
The gang gains initial access by a number of methods, but most usually via compromised credentials (most likely purchased on the darknet), especially where multifactor authentication is not present. The group has also been observed using phishing emails and malicious websites.
“Once infected, the malware will launch PowerShell to remove shadow volume copies, and once encryption is complete, the file’s extension will be reassigned with the ‘.akira’ extension,” the HSCCC report said.
“The attackers also attempt lateral movement and privilege escalation through LSASS credential dumps.”
While many gangs have recently begun to eschew encryption of target data and instead now rely on straight extortion, Akira still operates a double-extortion model, both exfiltrating data before encrypting it. A ransom note text file is left behind. During an attack, Akira uses a number of different tools, including the PCHunter toolkit, port scanner MASSCAN, and Mimikatz for credential harvesting.
The note itself offers a number of payment options, including one where the victim does not get the decryption key, but Akira promises not to post the stolen data. The group also offers “exclusive firsthand information” relating to the ransomware attack so that victims can patch up the vulnerabilities it had taken advantage of.
Like many groups, Akira sees itself as offering a service to its victims.
Links to Conti
The Conti ransomware group began operation in 2020, operating a ransomware-as-a-service model. The group was known for targeting healthcare organisations, particularly in New Zealand.
The group began to fall apart during Russia’s invasion of Ukraine, when Conti came out publicly supporting Russia and its aims. However, soon after, an unknown individual quickly leaks large volumes of chat logs and the group’s source code in protest. The leaked messages laid open the group’s operations and possible links with the Russian FSB.
The group disbanded weeks later.
The code used by Akira in its 2023 operations has a significant overlap with Conti source code, and Akira uses the same list of file exceptions when it comes to encryption.
Researchers have also noted an overlap in the cryptocurrency wallets used by the two groups.
“In a pattern analysis of cryptocurrency wallets, researchers were able to identify overlap in the wallets between Akira and Conti,” the report read. “In two of these transactions, the wallets had previously been affiliated with Conti’s leadership team.”
Regardless of any fetish for retro computing, and despite lacking the advanced toolsets of some other ransomware operators, Akira remains an active threat to organisations in the healthcare, finance, manufacturing, and real estate sectors.
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.
David Hollingworth
David Hollingworth has been writing about technology for over 20 years, and has worked for a range of print and online titles in his career. He is enjoying getting to grips with cyber security, especially when it lets him talk about Lego.