Based on data from Avanan's new attack brief, the researchers have found threat actors are creating phishing pages on AWS using the site's legitimacy to steal credentials.
Amazon Web Services (AWS) is one of the most popular cloud storage and hosting solutions, from major companies hosting their work on the service, to individuals using the platform to create and host webpages. Avanan researchers have noted that "if you’re using a site on the internet, there’s a good chance that AWS is involved in some fashion".
In this attack, hackers are creating phishing websites using AWS apps.
Vector: Email
Type: Credential Harvesting
Techniques: Static Expressway
Target: Any end user
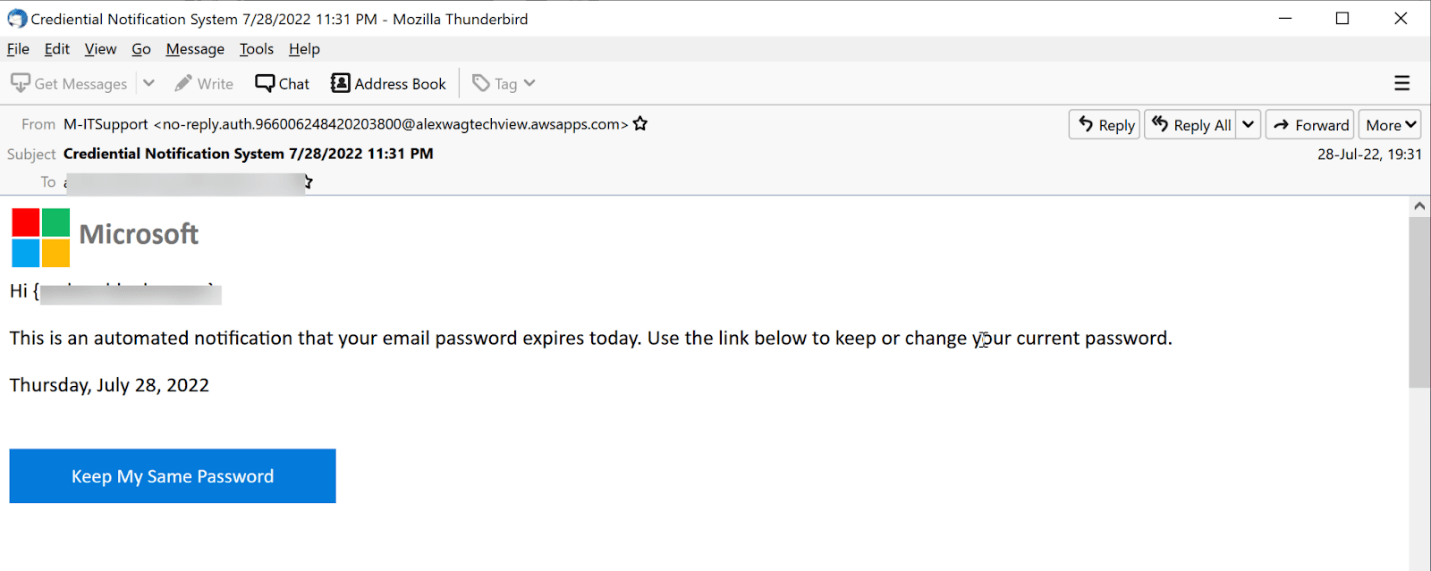
The user is presented with what looks like a standard password expiration email.
Avanan researchers noted that "when looking at the email under the hood, a few things stand out" in this example.
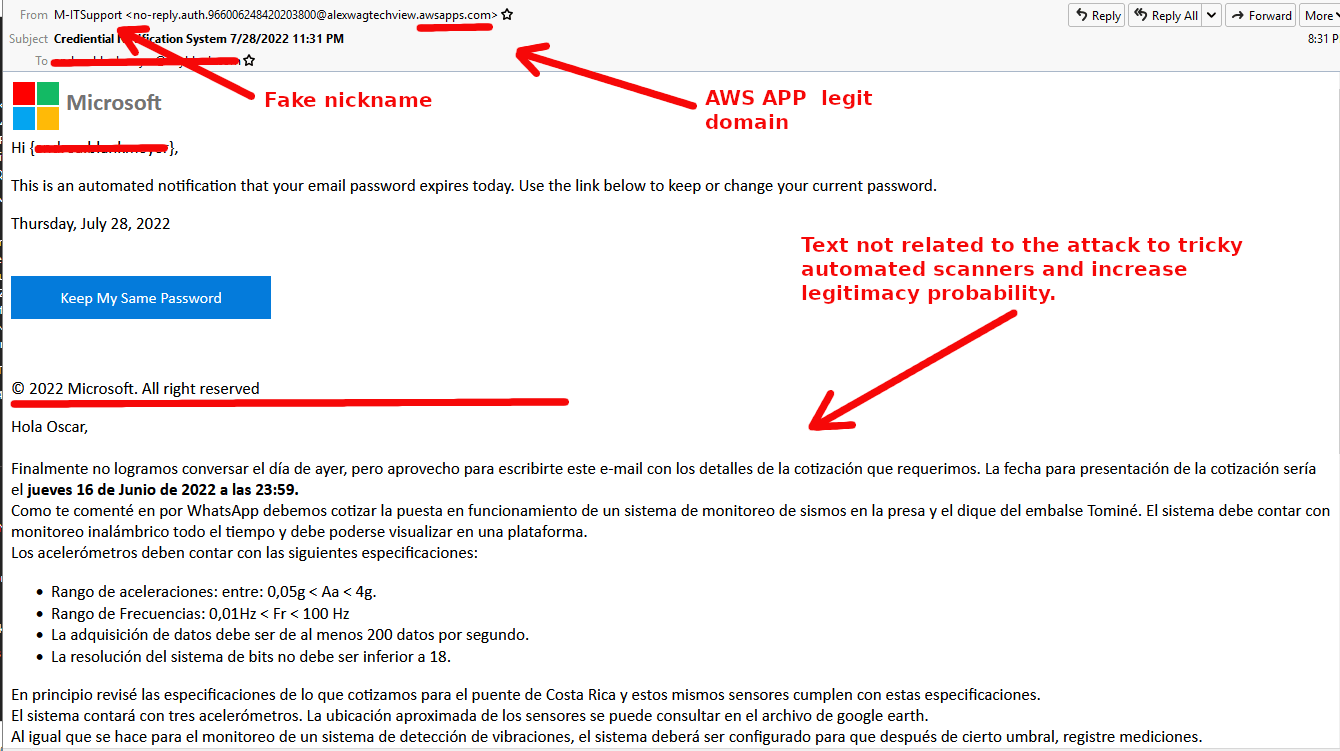
First-up, there is a fake nickname with the sender address, however, the domain is a legitimate AWS domain.
The text is not related to the attack. The email in question is in Spanish, but here is a rough translation of part of it:
Hello Oscar,
Finally we did not manage to talk yesterday, but I take the opportunity to write you this e-mail with the details of the quote that we require. The date for submitting the quote would be Thursday, June 16, 2022 at 11:59 p.m.
As I told you on WhatsApp, we must quote the start-up of an earthquake monitoring system in the dam and the dam of the Tominé reservoir. The system must have wireless monitoring at all times and must be viewable on a platform.
This, obviously, has nothing to do with a password reset, the Avanan researchers added.
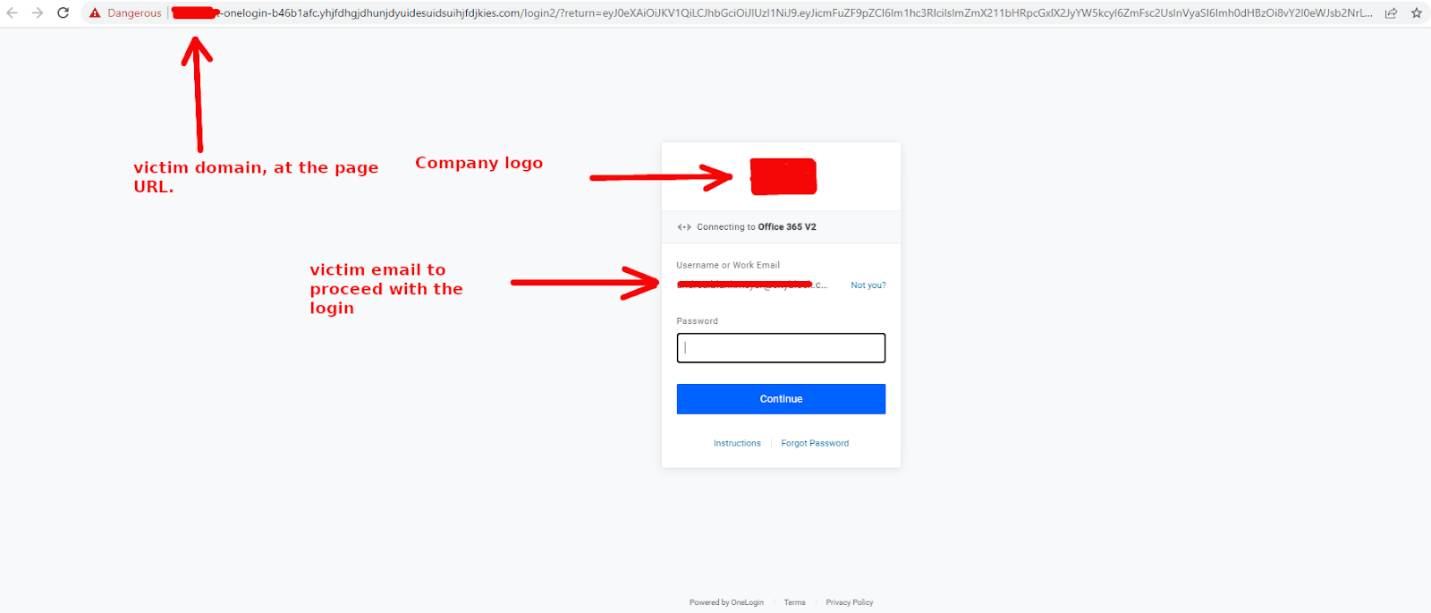
Finally, when clicking on the link, the user is redirected to a log-in page. The domain of the victim’s company is there, so is the email pre-populated and the company logo. All the user has to do is fill in their password and their credentials are stolen.
The Avanan researchers further explained that in order to get into inboxes, hackers will do whatever they can.
Recently, there has been a significant uptick in attacks using legitimate services as a piggyback to land in an inbox, known as "The Static Expressway".
Email services that use static "allow or block lists" to determine if email content is safe or not, are far from being immune to these attacks.
Essentially, these services are designed to determine whether a website is safe or not, however, Amazon Web Services will always be marked as safe. It's too big and too prevalent to block. Avanan researchers note that they have "seen this example with Google, QuickBooks, PayPal and much more".
This particular example uses AWS to send and host a phishing email. A static solution will not block something from AWS, and the email comes from a legitimate domain. The giveaway is that the email content is all over the place, which is intentionally done to confuse scanners.
Guidance and recommendations
To guard against these attacks, Avanan researchers suggest the following:
- Always hover over any link to see the destination URL before clicking on it.
- Encourage end users to ask IT if the email is legitimate or not.
- Always look at the content of the email before proceeding.
Leveraging on the fairly simple way to get into inboxes, plus a low lift from end users, this type of attack can prove to be quite successful for hackers.
Avanan notified AWS of these findings and will update with any additional information.
[Related: ANZ organisations incapable of breach detection within 90 days, report reveals]
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.

