The AFP was able to identify the alleged Australian offenders who bought the remote access Trojan (RAT) but also identified the Australian victims who were targeted through Operation Cepheus, "in a world-first for any law enforcement agency".
The man, now based in Melbourne, was 15 years old when he allegedly created the RAT, is facing six charges for his alleged role in creating, selling and administering the RAT between 2013 and 2019. He was scheduled to appear in Brisbane Magistrates Court on 29 July 2022, but the matter was adjourned until 19 August 2022.
The AFP identified there were 201 individuals in Australia who bought the RAT.
The AFP will allege the man engaged with a network of individuals and sold the spyware, named Imminent Monitor (IM), to more than 14,500 individuals across 128 countries. While it was not unlawful to buy the RAT in Australia, it is a crime to install the spyware on a victim's computer without their consent.
The RAT cost about AU$35 (US$25) and was allegedly advertised on a forum dedicated to hacking.
The spyware could be installed via a number of methods like phishing. Once the RAT had been installed in the victim's computer, users could control a victim's computer, steal their personal information or spy on them by turning on webcams and microphones on devices, all without their knowledge. It was also capable of logging keystrokes, which means users could see what was being written in the victim's emails and other documents – such as the home address of a victim. The AFP believes there were tens of thousands of victims globally.
A statistically high percentage of Australia-based PayPal purchasers of IM RAT (14.2 per cent) are named as respondents on domestic violence orders. Additionally, one of these purchasers is also registered on the Child Sex Offender Register.
Disturbingly, 11 individuals bought the RAT during the active period of their domestic violence order (DVO) or within two years a DVO was issued.
Chris Goldsmid, AFP Commander Cybercrime Operations, noted that cyber jobs could often be abstract for many in the community, but Operation Cepheus provided clear and real examples of how dangerous tech-enabled crime could be.
"These types of malware are so nefarious because it can provide an offender virtual access to a victim's bedroom or home without their knowledge.
"Unfortunately, there are criminals who not only use these tools to steal personal information for financial gain but also for very intrusive and despicable crimes.
"One of the jobs for the AFP is to educate the public about identifying and protecting themselves from spear-phishing attacks or socially-engineered messaging – essentially emails or texts messages that trick individuals into uploading malware," Commander Goldsmid said.
Operation Cepheus began when the AFP received information from cyber security firm Palo Alto Networks and the FBI about a suspicious RAT in 2017, which sparked a global investigation including more than a dozen law enforcement agencies in Europe. Eighty-five search warrants were executed globally, with 434 devices seized and 13 people arrested for using the RAT for alleged criminality.



A team of five AFP cyber crime investigators shut down the RAT in 2019, it stopped operating on all devices across the globe.
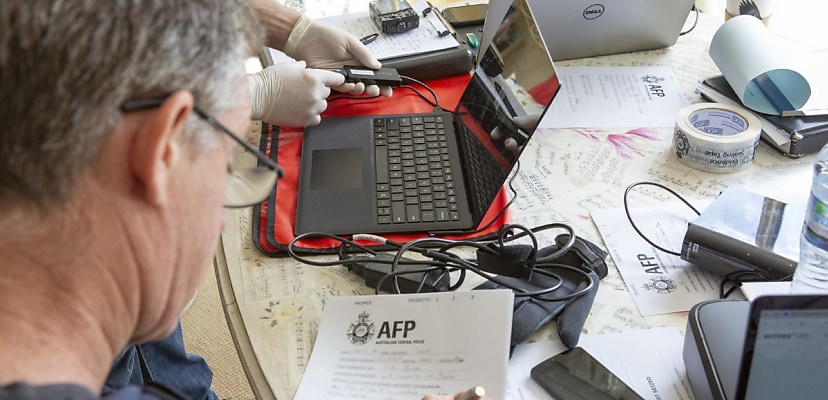
Following the receipt of admissible evidence from overseas law enforcement agencies within the same year, the AFP was able to arrest the Melbourne man who created the RAT. AFP Investigators seized a number of devices from the man's previous home in Brisbane, including a custom-built computer containing code consistent with the development and use of the RAT. Allegedly, the man made between $300,000 and $400,000 from selling the malware.
Commander Goldsmid noted that the AFP is a global leader in fighting cyber crime who worked closely with its international partners to ensure developers and users of "insidious malware" would be brought to justice.
"This outcome is the culmination of years of collaboration between the AFP and its international partners, trawling through thousands of pieces of data to bring to account those who are responsible for breaching the privacy of innocent people,” Goldsmid said.
The man is facing a maximum penalty of 20 years’ imprisonment for all the offences combined.
[Related: China’s influence campaigns, changing the way we think]
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.
Nastasha Tupas
Nastasha is a Journalist at Momentum Media, she reports extensively across veterans affairs, cyber security and geopolitics in the Indo-Pacific. She is a co-author of a book titled The Stories Women Journalists Tell, published by Penguin Random House. Previously, she was a Content Producer at Verizon Media, a Digital Producer for Yahoo! and Channel 7, a Digital Journalist at Sky News Australia, as well as a Website Manager and Digital Producer at SBS Australia. Nastasha started her career in media as a Video Producer and Digital News Presenter at News Corp Australia.