The Check Point Research (CPR) Q2 Brand Phishing Report highlighted the brands that were most frequently imitated by cyber criminals. Social media platform LinkedIn topped the list, continuing its reign as the most imitated brand after entering the rankings for the first time in Q1.
According to CPR researchers, while LinkedIn's share has dropped slightly, down from 52 per cent in Q1 to 45 per cent of all phishing attempts in Q2, it is "still a worrying trend" that has revealed the ongoing risks facing users of the trusted social media platform.
The CPR data shows social networks generally continue to be the most imitated category, followed by technology, which took over second place from shipping this quarter.
According to Omer Dembinsky, data research group manager at Check Point Software, phishing emails are prominent tools in every hacker's arsenal as these are fast to deploy and can target millions of users at a relatively low cost.
"They give cyber criminals the opportunity to leverage the reputation of trusted brands to give users a false sense of security that can be exploited to steal personal or commercial information for financial gain.
"The criminals will use any brand with sufficient reach and consumer trust.
"Hence, we see hackers expanding their activities with the first appearance of Adidas, Adobe, and HSBC in the top 10. The hackers trade on our trust in these brands and that very human instinct for 'the deal'," Dembinsky explained.
The data has revealed a rise in exploitation of technology household names which include Microsoft, making up 13 per cent of all brand phishing attempts, more than double the amount in the previous quarter, and DHL took third place with 12 per cent. New brands that entered the CPR top 10 included Adidas, Adobe and HSBC. Although all on low single digits, the CPR researchers explained these brands will be followed closely in Q3 for developments.
The increase in the use of Microsoft-related scams is a danger to both individuals and organisations, the CPR researchers further explained.
"Once someone has hold of your account login details, they have access to all the applications behind it, such as Teams and SharePoint, as well as the obvious risk of compromise to your Outlook email account.
"The report highlights a specific example of an Outlook phishing email luring users to a fraudulent Outlook web page with the subject line: "[Action Required] Final Reminder - Verify your OWA Account now", asking the victim to enter their login credentials."
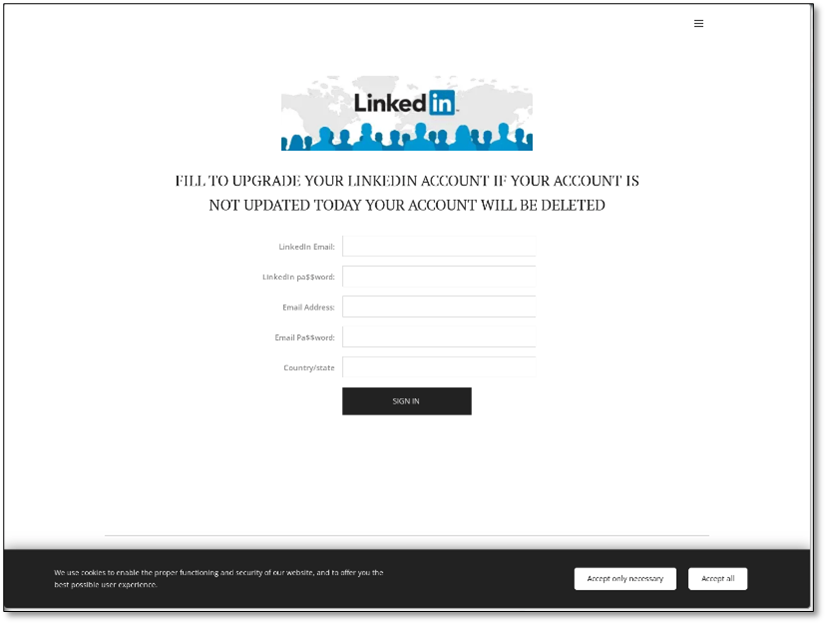
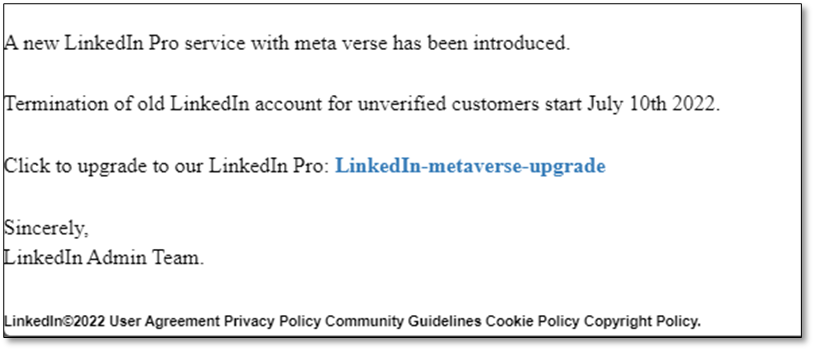
The CPR researchers added that although phishing communications appear to come from LinkedIn, the email address used is completely different to that of the brand.
"LinkedIn-based phishing campaigns imitated the style of communication of the professional social media platform with malicious emails using subjects like: 'You appeared in 8 searches this week' or 'You have one new message' or 'I’d like to do business with you via LinkedIn'," the CPR researchers said.
The Q2 results also saw shipping company DHL being faked in 12 per cent of all phishing attacks, which isn't a surprise due to the continuing trend of online shopping.
The CPR report specifically references a tracking-related phishing scam, with the subject line "Incoming Shipment Notification," enticing the consumer to click on a malicious link.
Ranked by their overall appearance in brand phishing attempts, the top brands in Q2 2022 are:
- LinkedIn (45 per cent);
- Microsoft (13 per cent);
- DHL (12 per cent);
- Amazon (9 per cent);
- Apple (3 per cent);
- Adidas (2 per cent);
- Google (1 per cent);
- Netflix (1 per cent);
- Adobe (1 per cent); and
- HSBC (1 per cent).
A brand phishing attack not only takes advantage of our implicit trust in a familiar brand, adopting its brand imagery often using a similar URL. The CPR researchers added that it also plays on human emotions, like the fear of missing out on a discount. The sense of urgency this creates leads consumers to click in haste without first checking if the email is from the brand in question. This could lead to inadvertently downloading malware or handing over precious personally identifiable information which can give criminals access to their entire online world and potential financial loss.
According to Dembinsky, there's a reason the hackers continue to use brand-based phishing.
"It works.
"So, consumers need to act with caution and look out for telltale signs of the fake email, like poor grammar, spelling mistakes or strange domain names.
"If in doubt, head for the brand's own website rather than clicking any links," Dembinsky concluded.
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.

