PIPEDREAM is the seventh known industrial control system (ICS)-specific malware. PIPEDREAM is a modular ICS attack framework that an adversary could leverage to cause disruption, degradation, and possibly even destruction depending on targets and the environment.
Since early 2022, Dragos has been analysing the PIPEDREAM toolset, which is the seventh ever ICS specific malware, according to Dragos analysts.
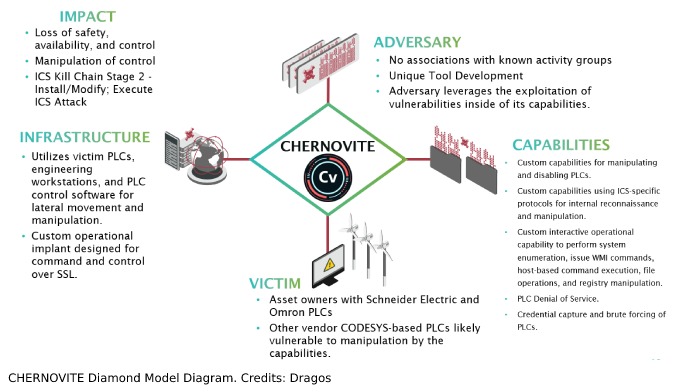
“We track its developers as the threat group CHERNOVITE, which we assess with high confidence to be a state actor that developed the PIPEDREAM malware for use in disruptive or destructive operations against ICS.
“Specifically, the initial targeting appears to be liquid natural gas and electric community specific.
“However, the nature of the malware is that it works in a wide variety of industrial controllers and systems,” Dragos analysts said.
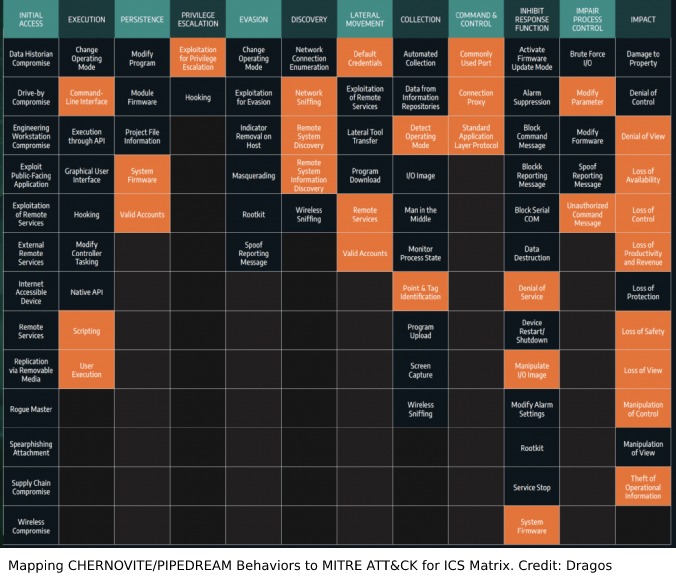
CHERNOVITE’s PIPEDREAM can execute 38 per cent of known ICS attack techniques and 83 per cent of known ICS attack tactics.
PIPEDREAM can manipulate a wide variety of industrial control programmable logic controllers (PLC) and industrial software, including Omron and Schneider Electric controllers, and can attack ubiquitous industrial technologies including CODESYS, Modbus, and Open Platform Communications Unified Architecture (OPC UA). Together, PIPEDREAM can affect a significant percentage of industrial assets worldwide.
PIPEDREAM is not currently taking advantage of any Schneider or Omron vulnerabilities, instead it leverages native functionality.
While CHERNOVITE is specifically targeting Schneider Electric and Omron PLCs, there could be other modules targeting other vendors as well, and PIPEDREAM’s functionality could work across hundreds of different controllers. The focus on the equipment vendor is misplaced, and instead the focus should be placed on the tactics and techniques the adversary is leveraging.
PIPEDREAM accomplishes this far-reaching impact through a series of five components that Dragos labels:
- EVILSCHOLAR
- BADOMEN
- DUSTTUNNEL
- MOUSEHOLE
- LAZYCARGO
These combined components allow CHERNOVITE to enumerate an industrial environment, infiltrate engineering workstations, exploit process controllers, cross security and process zones, fundamentally disable controllers, and manipulate executed logic and programming.
All of these capabilities can lead to a loss of safety, availability, and control of an industrial environment, dramatically increasing time-to-recovery, while potentially placing lives, livelihoods, and communities at risk.
Due to the historic and expansive nature of PIPEDREAM, mitigating the CHERNOVITE threat will require a robust strategy, and not simply applying cyber security fundamentals. Dragos recommends the following defensive mitigations.
Dragos analysts further explained that the PIPEDREAM malware initially targeted Schneider Electric and Omron controllers, however there are not vulnerabilities specific to those product lines.
“PIPEDREAM takes advantage of native functionality in operations, making it more difficult to detect.
“It includes features such as the ability to spread from controller to controller and leverage popular ICS network protocols such as ModbusTCP and OPC UA,” Dragos analysts said.
Recommendations
- Monitor industrial environments for all threat behaviours in the MITRE ATT&CK for ICS matrix as adversaries are increasing their scope and scale of capabilities.
- Ensure ICS visibility and threat detection include all ICS North-South and East-West communications – network edge and perimeter monitoring are insufficient for PIPEDREAM.
- Maintain knowledge and control of all assets within operational technology (OT) environments, including details such as ensuring only known-good firmware and controller configuration files are in use.
- Utilise a fully researched and rehearsed industrial incident response plan that includes attempts by adversaries to deny, disrupt, and destroy processes ensuring an extended time-to-recovery.
Uniquely, this malware has not been employed in target networks, the Dragos analysts further explained.
“This provides defenders a unique opportunity to defend ahead of the attacks.
“While the malicious capability is sophisticated with a wide range of functionality, applying fundamental ICS cyber security practices such as having a defensible architecture, ICS specific incident response plan, and ICS network monitoring provide a robust defence against this threat,” Dragos analysts concluded.
[Related: ANZ organisations moving towards DevSecOps]
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.

