The Vect ransomware group may have emerged only this year and claimed only a mere 25 victims in that time, but the ransomware-as-a-service operation is making ripples in the cyber criminal community.
The group allied with the hackers behind the recent Trivy and LiteLLM compromises, TeamPCP, to take advantage of delays in complete credential rotation.
In an effort to find new affiliates, Vect announced it would share login keys to any interested members of the BreachForums hacking community, which several members have taken advantage of.
Researchers at ThreatLocker’s Threat Intelligence team have also been able to get a cheeky look inside Vect’s affiliate program and its dashboard.
Serious business
Vect may be new, but it is already offering a whole host of features to would-be hackers via its affiliate dashboard.
In fact, Danny Jenkins, ThreatLocker CEO and co-founder, said Vect’s affiliate program illustrates the maturity of modern ransomware operations.
“The access we gained to the Vect platform shows the level of business discipline cyber criminals have developed, and that coordination among them continues despite the shutdown of other hubs they once relied on,” Jenkins told Cyber Daily.
“What we observed mirrors a modern SaaS operation, complete with help tickets, how-to guides, chat functionality, user outreach, and a well-defined affiliate program.”
The dashboard features everything a budding hacker could want. Some parts of the dashboard, like the news section, are currently empty, but others, like the global chat feature, are well populated.
In the latter’s case, ThreatLocker observed affiliates “actively communicating, supporting, and coordinating with each other”. Vect admins are also active in affiliate chats, providing answers to questions and motivational messages.
Similarly, a Teams function lets affiliates band together and share data. However, the meat of the dashboard is in the Builder and Earnings sections.
If you build it
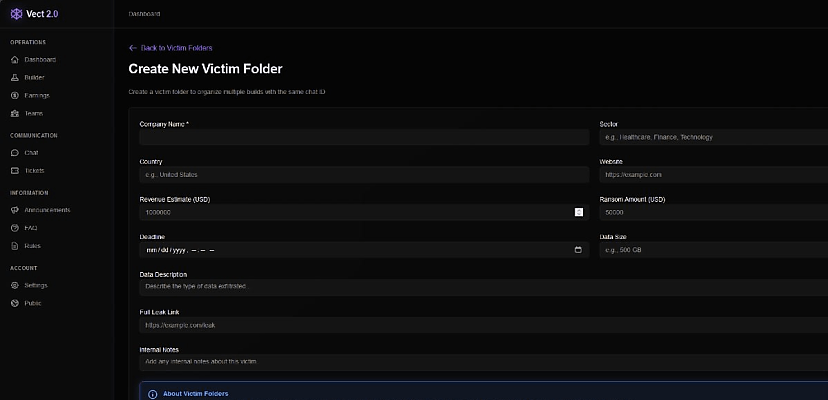
The Builder is where affiliates create victim profiles around which a custom encryptor will be built.
“The only required field is the company name, but several other fields allow specifics such as business sector, ransom amount, revenue estimate, and size of leaked data,” ThreatLocker said in a 28 April blog post.
“These details can later be edited and added to reflect negotiations.”
Chat IDs can be created so victims can communicate with their hackers, and the encryptor itself offers three build options targeting different OSes: Windows, Linux, and ESXI. A fourth option, an exfiltration-only binary, is currently listed as coming soon, suggesting Vect is actively developing its capabilities.
The Earnings part of the dashboard lets affiliates keep track of their ill-got gains. Newcomers to Vect can earn an 80 per cent commission (the rest goes to Vect itself), but they can also progress through five levels as they bring in more and more ransom payments.
For instance, once an affiliate earns US$75 million, they reach the highest level, five, at which point their commission bumps up to 89 per cent.
The dashboard also features a Tickets page, where affiliates can submit support tickets.
Announcements, an FAQ, and community rules also all have their own sections, though they are currently empty. Finally, the Account Settings section lets affiliates choose between three languages – English, Russian, and Chinese – and set up 2FA authentication to secure their account.
ThreatLocker said its investigation revealed the “scale and accessibility” of Vect’s growing operation.
“The dashboard remains active and functional, reinforcing a broader shift in the ransomware landscape: Threat actors are no longer relying on their core team to compromise victims,” the researchers said.
“Instead, they are embracing a ransomware-as-a-service model, trading a lower share of the extorted funds for a much higher volume of victims.”
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.
David Hollingworth
David Hollingworth has been writing about technology for over 20 years, and has worked for a range of print and online titles in his career. He is enjoying getting to grips with cyber security, especially when it lets him talk about Lego.