While some ransomware gangs at least try to adhere to picking their targets with a bare minimum of compassion, the Medusa ransomware gang has no such qualms.
Since launching its .onion-based leak site in early 2023, the group has not shied away from targeting healthcare entities or not-for-profit organisations. In fact, its latest victim is Water for People, a US-based not-for-profit focused on providing clean drinking water to communities in developing countries.
Just when you think cyber criminals can’t go any lower, here we are.
But who is Medusa, and how does it go about its operations?
Leak site operations
First up, we can say who Medusa isn’t – it’s probably easier than saying who they are, actually. Though they share a name, the ransomware gang does not appear to have any links to the MedusaLocker ransomware-as-a-service platform, according to Unit42, which recently dedicated a blog post to the gang. MedusaLocker has been on the scene since at least 2019, while Medusa, in its current form, rose to prominence in early 2023 when it set up its dark web leak site.
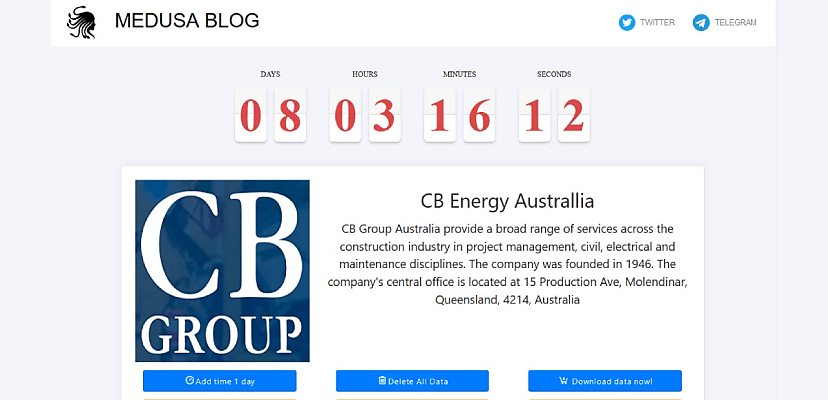
It uses that site to extort its victims, threatening to publish purloined information if a ransom payment is not forthcoming. Victims are given three options when it comes to dealing with the gang: they can pay a smaller amount to extend the ransom deadline by 24 hours or pay the full amount to either have the data deleted entirely or download the data itself. The leak site, like many others, features a viewer counter to apply further pressure, showing a victim exactly how many people have been looking at its particular leak page.
Medusa typically shares a few files to prove the hack is the real deal. The group also appears to have employed its own Medusa Media Team. A recent post included a video of compromised files, which is a new tactic for the gang.
The group also employs a Telegram page to share its exploits, though this is not Medusa-branded and often refers to Medusa as a separate entity.
“It’s unclear at the time of writing this article if the owner of this channel is part of the ransomware operation per se,” Unit 42’s researchers said in a blog post. “We do know that the platform is being leveraged to announce compromises and release exfiltrated information.”
Victimology
Looking at the organisations targeted by Medusa in the last 24 months suggests the group is largely opportunistic and purely financially motivated.
Tech companies, education, and manufacturing are the three most targeted sectors, but none of these reach double figures, and Medusa’s other victims include businesses in healthcare (which is a close fourth), hospitality, media, insurance, mining, and many more.
Similarly, while the majority of victims are US, UK, and French entities, many smaller countries have been impacted, again suggesting what Unit 42 calls an “indiscriminate approach”. While 24 of Medusa’s victims have been American organisations, countries like Bolivia, Portugal, and Serbia have all been touched by the group’s activities.
Two Australian organisations have fallen victim to Medusa in the last 12 months – the Crown Princess Mary Cancer Centre in Sydney and the Gold Coast-based CB Group, a civil engineering firm. Medusa also appears to be responsible for briefly taking Auckland Transport offline in September 2023.
Anatomy of a Medusa attack
Unit 42 has the advantage of having worked as an incident response following one of its attacks. While the group has been observed to use several techniques to gain access to victim networks, including using access brokers and taking advantage of known vulnerabilities, it also uses some unique tactics.
In the particular incident that Unit 42 worked on, Medusa was seen uploading a web shell to a previously exploited Microsoft Exchange Server. Once that’s done, the gang uses PowerShell to run a bitsadmin transfer from an external hosting site, which – once the file is unpacked and executed – installs ConnectWise, a legitimate IT service management platform.
Two drivers are also dropped onto targeted networks to evade security software, each with their own loader. One driver looks for specific security processes, while the other is responsible for killing them.
Medusa then uses Netscan – a standalone version of the SoftPerfect Network Scanner, according to the Cybersecurity and Infrastructure Security Agency (CISA) – alongside a .xml file to enumerate the network. The scripts included in this process are in Cyrillic, which could suggest a country of origin for Medusa’s members.
Once a device has been discovered, the user can then simply right-click, and from then on, it’s largely a point-and-click operation with some interesting twists.
The everlasting gaze
The Medusa ransomware binary uses the term “gaze” a hell of a lot, showing at least a passing familiarity with the mythological figure of the same name. Medusa’s gaze was known to turn all who she looked upon to stone, an apt analogy for a ransomware operation. The binary is able to differentiate what to encrypt and not decrypt, typically avoiding Windows folders Program Files.
“Medusa ransomware uses RSA asymmetric encryption for protecting the AES256 key used for encrypting a victim’s files,” according to Unit 42. “The AES256 key is set up using a 32-byte key and a 16-byte initialisation vector. The encrypted files are renamed with the extension .medusa.”
Finally, a document is left on the affected machine called !!read_me_medusa!!.txt.
Looking for Perseus
Medusa has shown itself to be both resourceful and ruthless, and while it may not have the impact or reputation of Clop or LockBit, there’s no denying that the group is a threat actor to watch.
“The emergence of the Medusa ransomware in late 2022 and its notoriety in 2023 marks a significant development in the ransomware landscape,” Unit 42 concluded.
“This operation showcases complex propagation methods, leveraging both system vulnerabilities and initial access brokers, while adeptly avoiding detection through living-off-the-land techniques.”
Sadly, we’re sure we’ll have more news of Medusa shortly.
 Want to see more stories from trusted news sources?
Want to see more stories from trusted news sources?Make Cyber Daily a preferred news source on Google.
David Hollingworth
David Hollingworth has been writing about technology for over 20 years, and has worked for a range of print and online titles in his career. He is enjoying getting to grips with cyber security, especially when it lets him talk about Lego.